i-doit INDITOR - Your ISMS for ISO certifications, BSI & NIS-2
An ISMS in 15 days
Clear processes and predefined catalogs ensure the practical implementation of regulatory requirements.
As a GRC solution "Made in Germany", i-doit INDITOR creates a
reliable basis for sustainable information security.
4.7/5 on Capterra | 2,000+ satisfied customers
i-doit INDITOR ISO: Your path to ISO 27001 certification
Structured implementation of standard requirements and audit-proof documentation
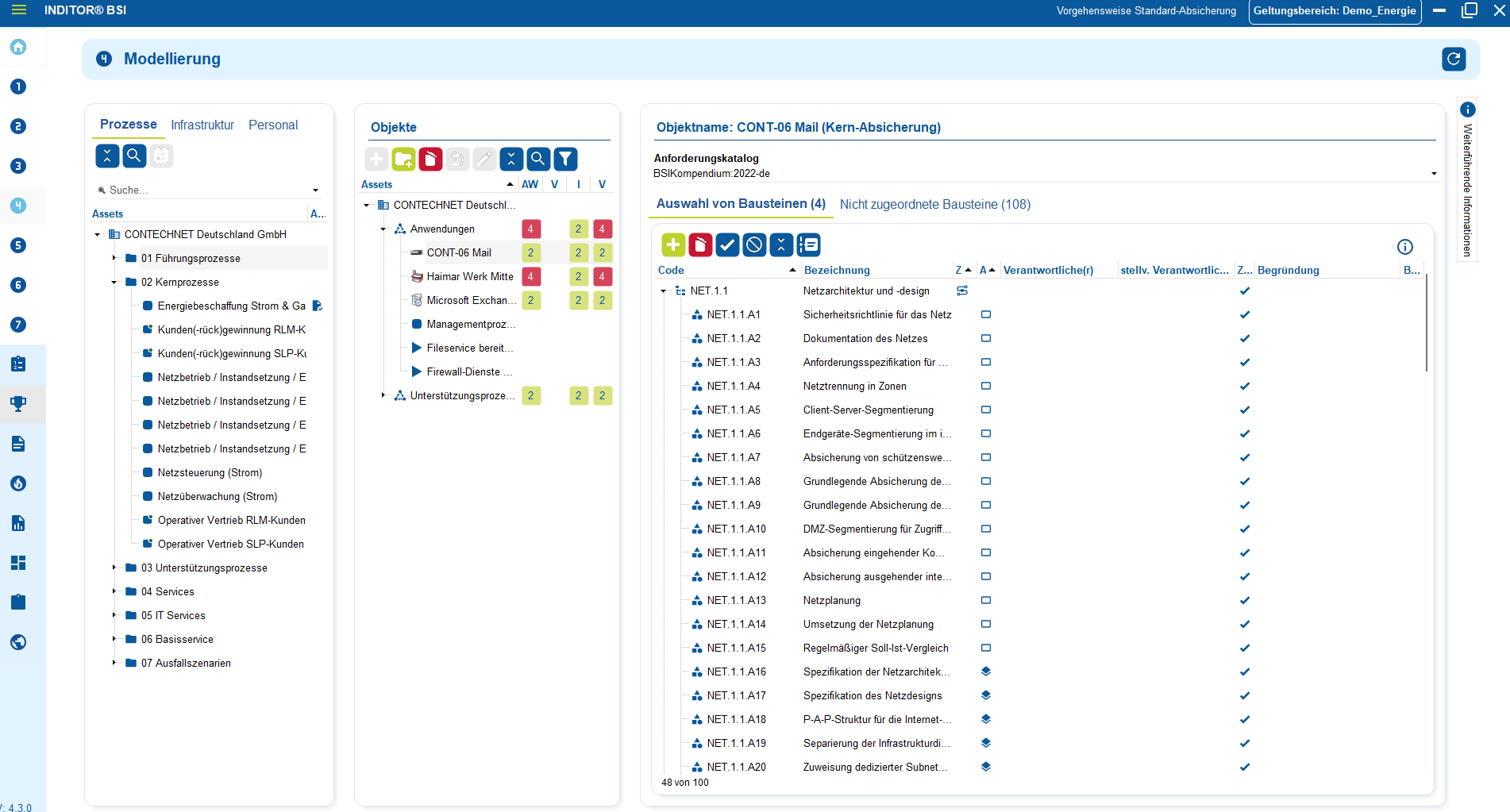
i-doit INDITOR BSI: Structured implementation of IT baseline protection
Centralized mapping and audit-proof documentation of requirements according to BSI IT-Grundschutz
i-doit INDITOR NIS-2: NIS-2-compliant & practically implemented
Central implementation with GAP analysis and audit-proof evidence
Catalogs
Advantages of our ISMS solution
Ready-made catalogs and templates
enable a quick start
All requirements, risks and measures
measures are centrally traceable
Structured processes reduce manual
activities and coordination
Not only introduce an ISMS, but
operate it effectively in the long term
Verification at any time
for tests and audits
Clear structures avoid gaps
and inconsistencies
All ISMS-relevant topics in a
common database
Easily scalable with growing requirements
Our editions for the i-doit INDITOR at a glance
The right ISMS solution for ISO, BSI and NIS-2 - transparent and clear
Use cases
Use cases relating to ISMS, risk and compliance management

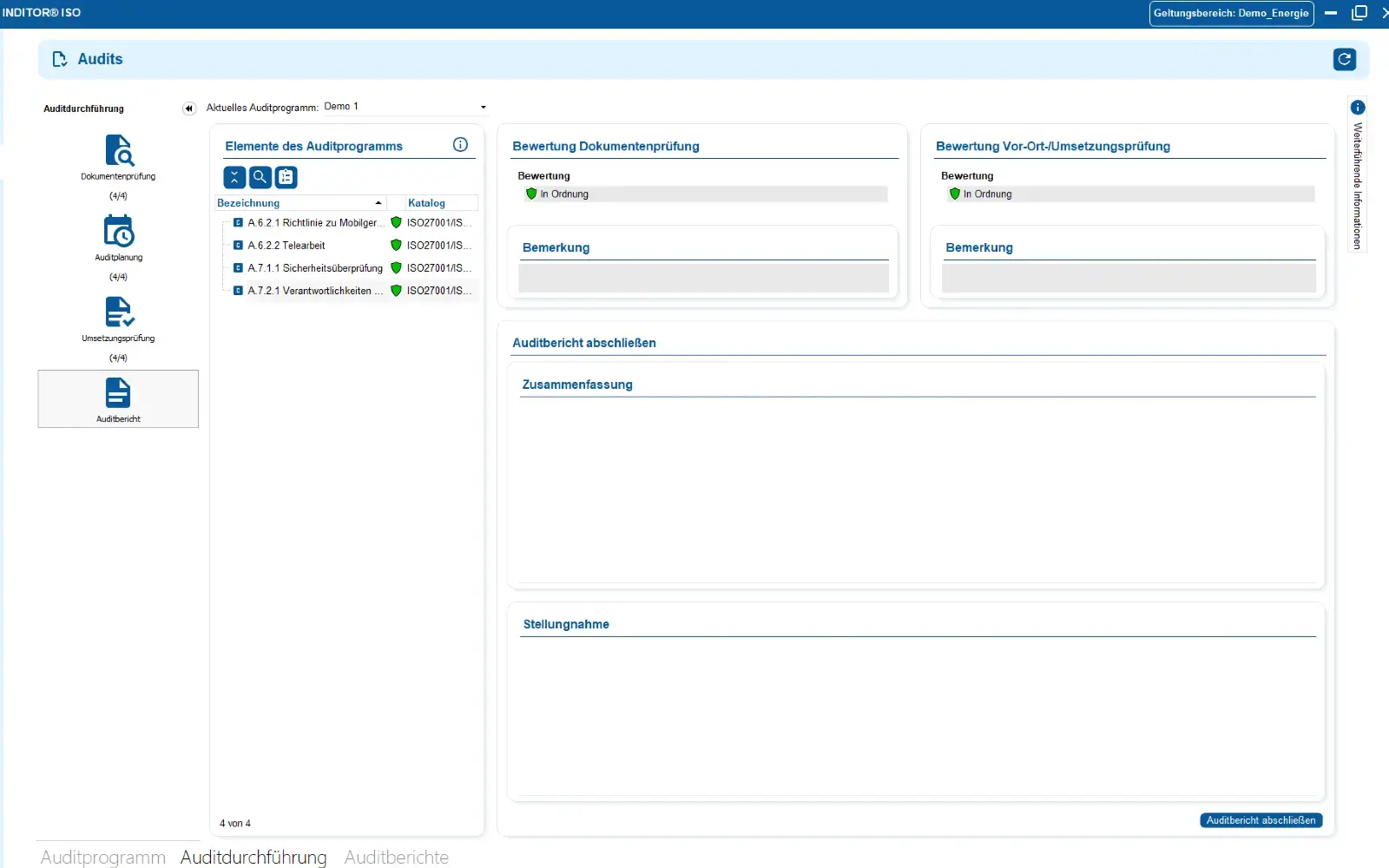
You control audits centrally, plan audits, document results and automatically generate audit reports.

You can manage documents in an audit-proof manner, version and edit them directly in the tool and use templates and import functions.

i-doit supports GAP analyses according to standards such as ISO 27001, ISO 9001 or NIS2, including maturity level assessment, responsibilities and document assignment.

You evaluate and manage suppliers centrally, document contracts and maintain contact details and replacement suppliers.

You derive measures, distribute tasks, track deadlines and receive automatic notifications by e-mail.

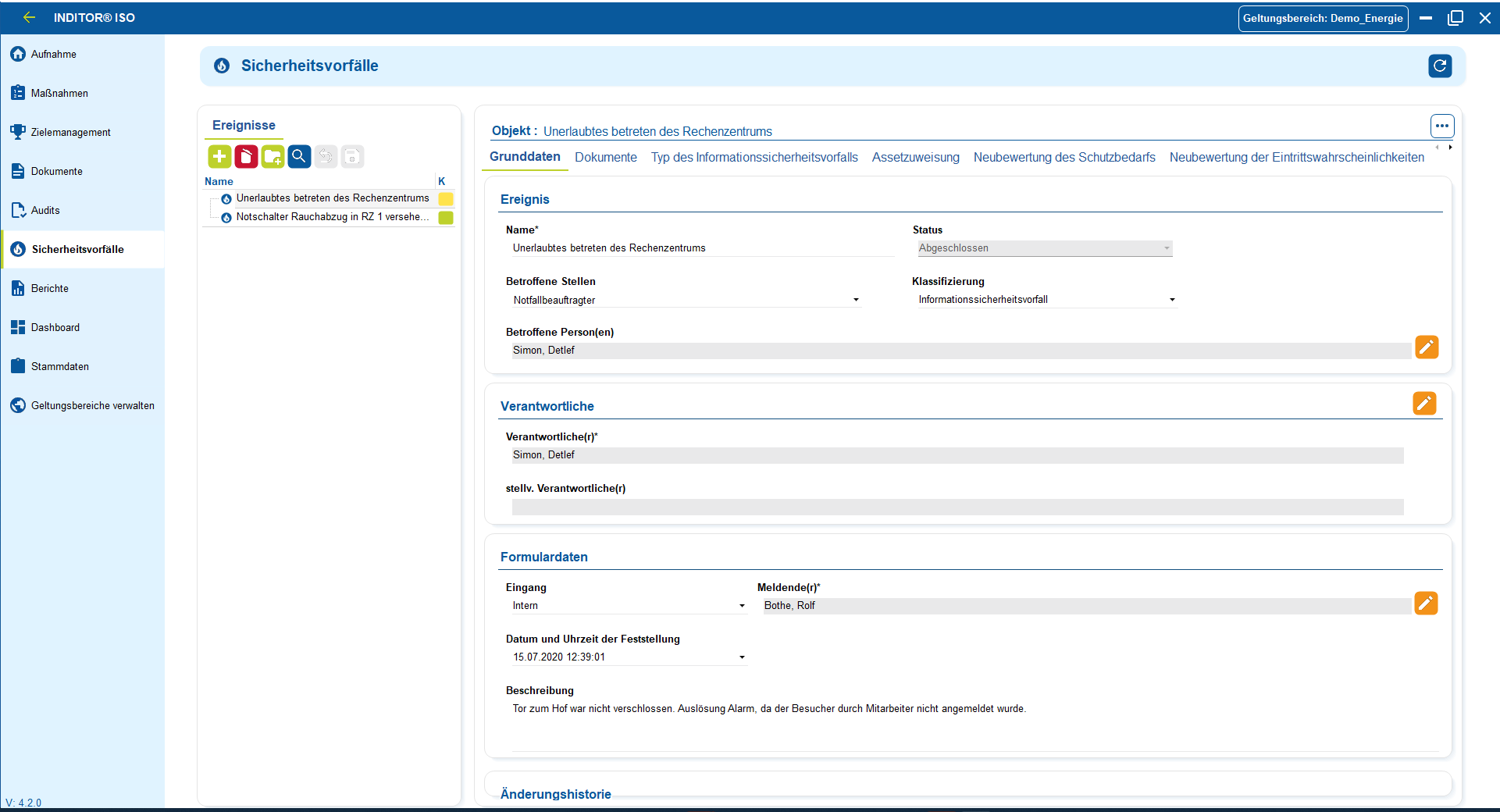
You document and evaluate security incidents in accordance with ISO and NIS2, assign affected assets and centrally derive measures.
.png?width=300&name=Contact%20(1).png)
Book your personal live demo
Our i-doit team will be happy to take the time to advise you personally on your application.
i-doit INDITOR Overview
The information security software that provides you with a guide
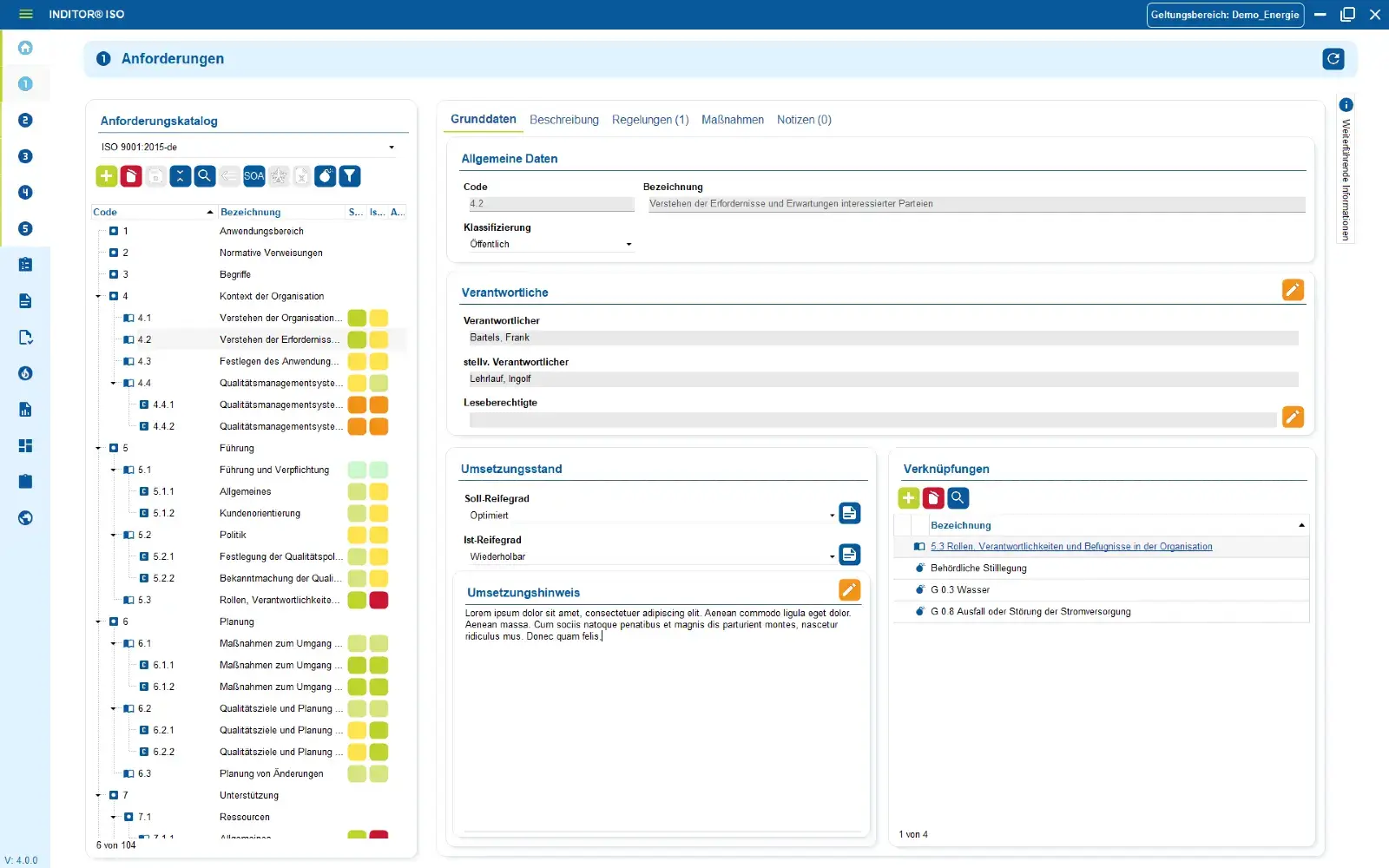
1. Catalog of requirements
Illustration of the requirements of the ISO / IEC 27001 catalog linked to the scope. The requirements and measures are supplemented in our ISMS tool i-doit INDITOR with implementation instructions and assistance. ISO / IEC 27002 is automatically linked.
Define responsibilities, implementation statuses and measures for individual requirements. Link guidelines (e.g. compliance) and documents relevant to the requirements and add implementation instructions.
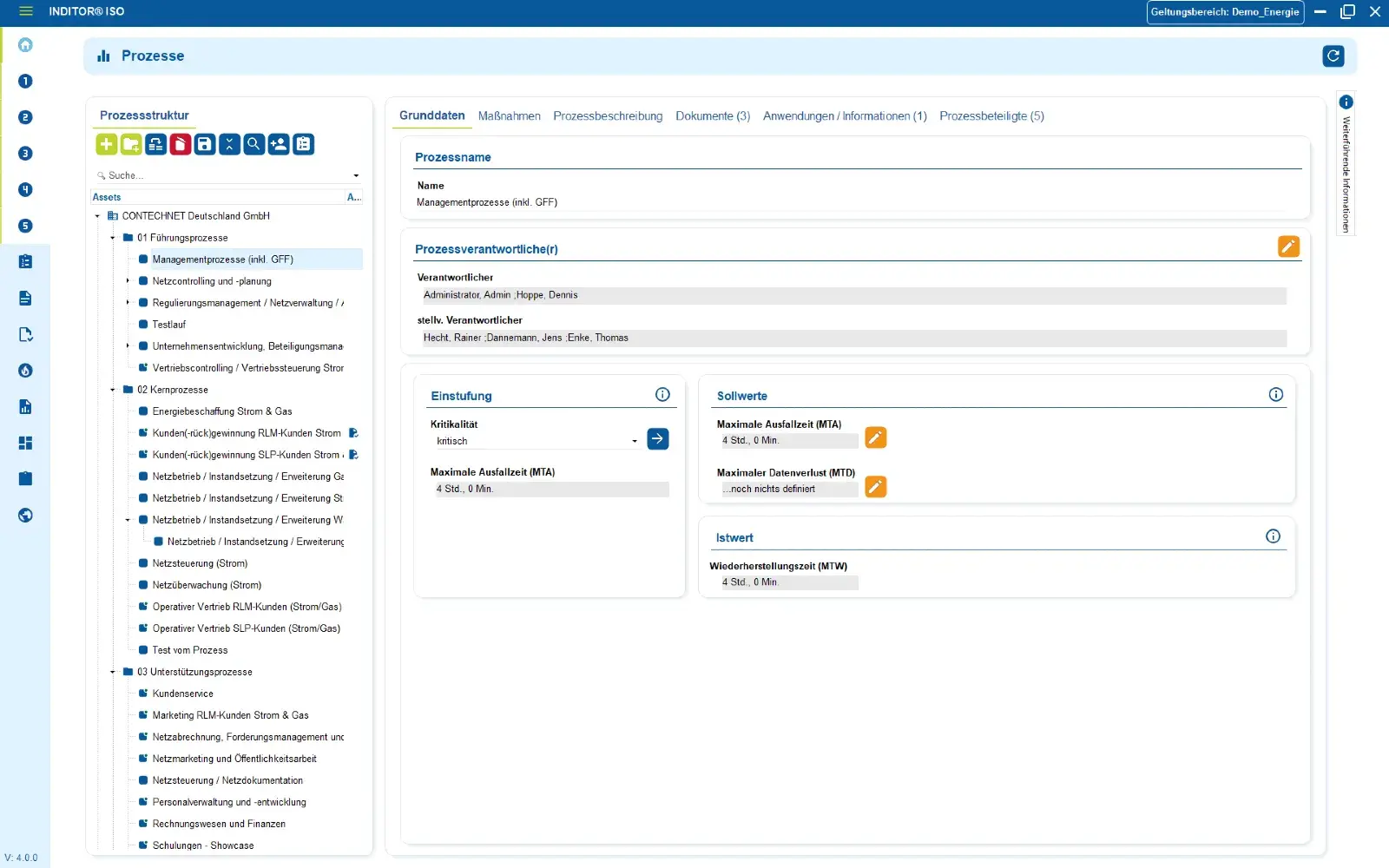
2. Asset management
With i-doit INDITOR ISO asset management, you can manage processes, personnel and IT infrastructure centrally. Included ISO-compliant standard processes can be expanded and imported. Asset trees, groups and dependencies support risk assessments in risk management. Existing inventory and IT solutions, suppliers and organizational units can be easily integrated. For maximum transparency in complex companies.
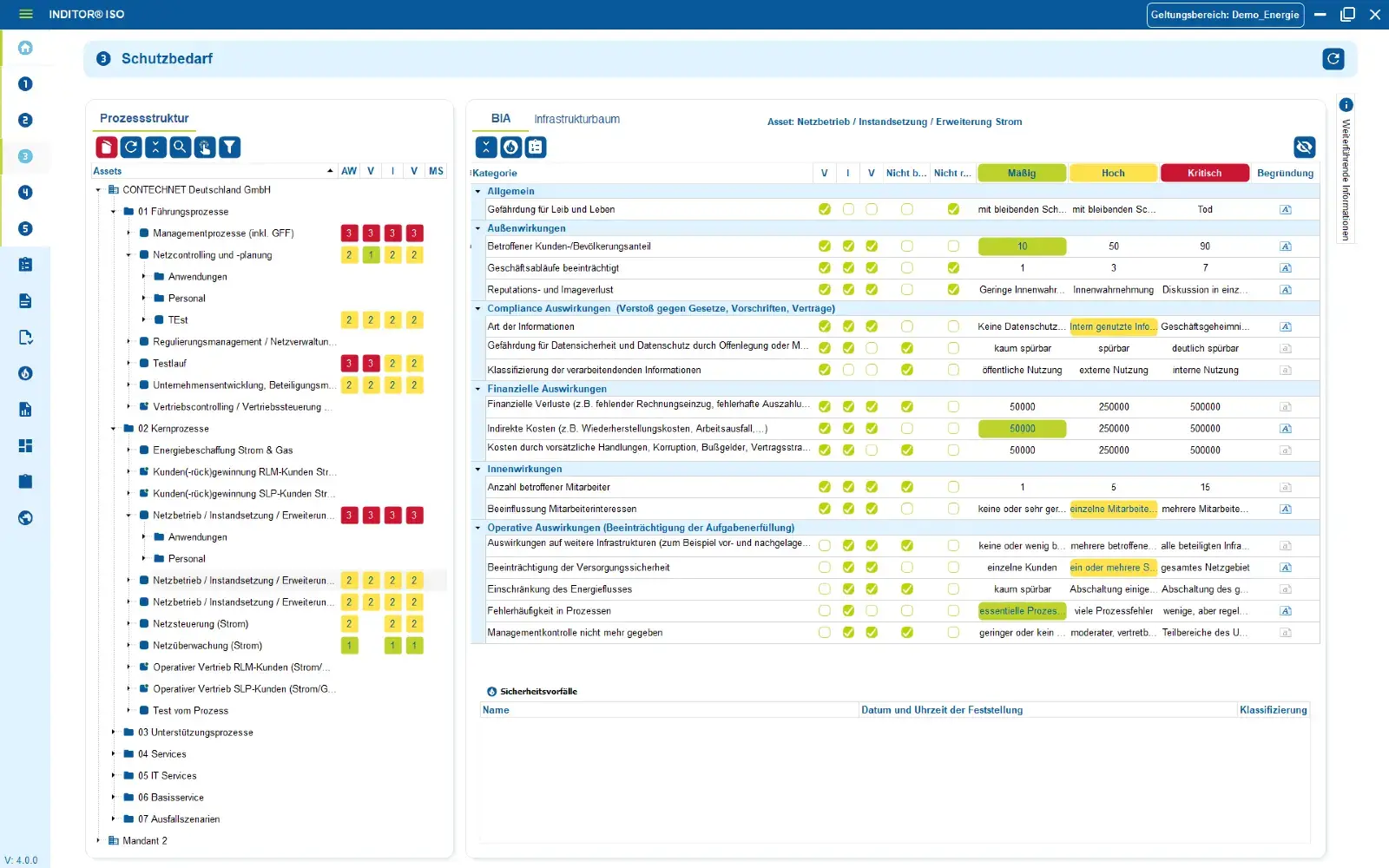
3. Determination of protection requirements
The protection requirement determines how important a process is for the functioning of all other processes in a company. You can make this determination in our software using a customizable Business Impact Analysis (BIA). This can be individually adapted to the circumstances and structures in your company.
The need for protection is automatically passed on to the people, applications and infrastructure it contains.
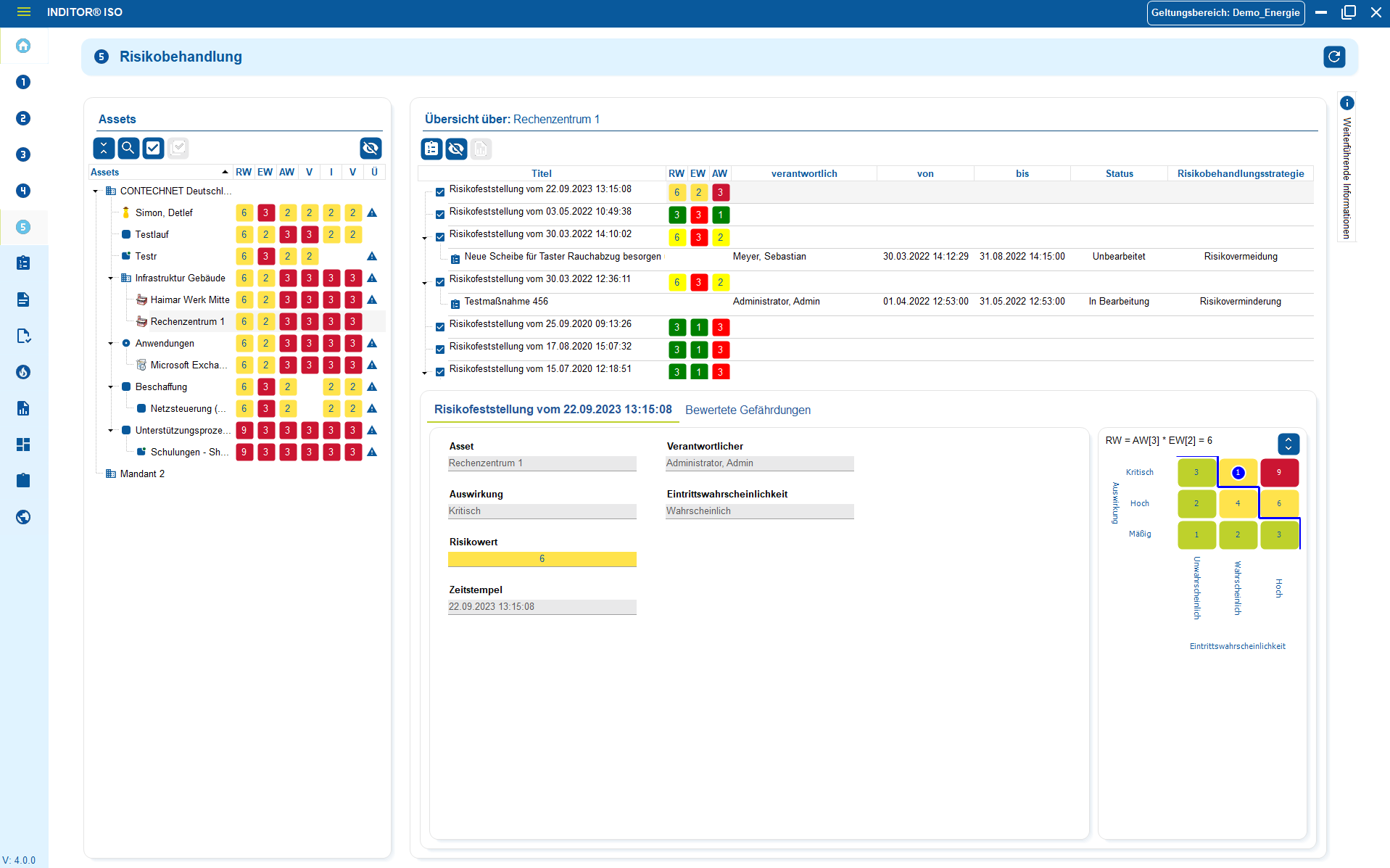
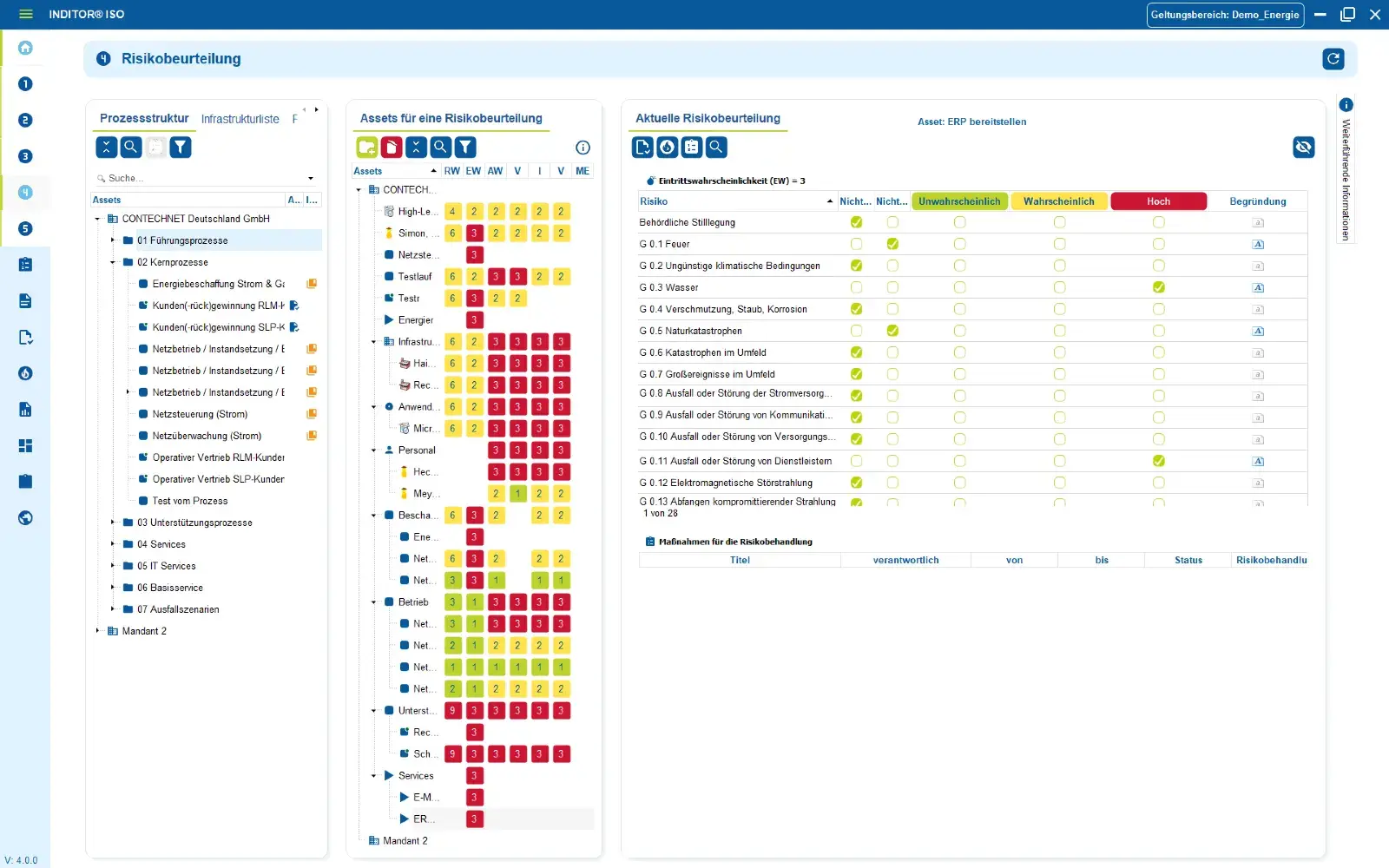
4. Risk assessment
In the risk assessment, you determine how high the probability of a risk occurring in a particular scenario is.
You assess the likelihood that these hazards will affect your company and the most probable consequences of this impairment for your company.
5. Audit management
Audit management is the ideal way to prepare for certification, e.g. to ISO/IEC 27001. You can plan and manage audits and check the current implementation status.
Compare security measures that have already been implemented with the requirements of the ISO standard to identify the level of security achieved and identify opportunities for improvement.
Industries
View all solutions for your industry



Read more




FAQs about i-doit INDITOR
Your advantages at a glance
An information security management system (ISMS) is a systematic approach to ensuring information security in organizations. It helps to identify and assess risks and implement suitable measures to secure processes and data - e.g. in accordance with ISO/IEC 27001.
The ISMS tool covers requirements from the following norms and standards, among others:
-
ISO/IEC 27001 & ISO/IEC 27002
-
Compliance catalogs (e.g. TISAX®, BAIT, VAIT, DIN EN ISO 9001 etc.)
-
Risk management, audit and action management including BIA (Business Impact Analysis)
The EU's NIS 2 Directive is a legal framework for increasing cyber security in critical sectors. It extends the requirements for security measures and reporting obligations for companies and organizations in the EU.
With the i-doit INDITOR NIS 2 module, i-doit offers a tool that maps the contents of the NIS 2 directive in a fully structured manner. Among other things, it supports
-
Clear inventory of the implementation status
-
Integrated GAP analysis/checklist for NIS2 compliance
-
Centralized management of responsibilities, evidence and measures
-
Audit-proof documentation for audit preparation
-
ISO 27001 is an international standard for a structured ISMS.
-
NIS2 is an EU directive with binding legal requirements on cyber security for affected organizations.
The NIS2 module uses an ISMS system as a technical platform to implement the directive efficiently.
IT baseline protection is an approach developed by the German Federal Office for Information Security (BSI) for a holistic information security management system. It comprises organizational, infrastructural and technical measures to secure systems and processes.
With i-doit INDITOR BSI, i-doit offers software for implementing IT baseline protection in accordance with the BSI standards (including 200-1, 200-2, 200-3). This solution:
-
maps the BSI specifications in a structured manner
-
enables risk management, documentation & task management
-
provides templates for guidelines and reports
-
supports individually customizable per scope
Yes, the -i-doit software has a modular structure and can be used flexibly:
-
Only individual modules (e.g. ISO-ISMS, NIS2 or IT-Grundschutz)
-
or integrated as part of a comprehensive information security management system with a shared database and standardized interface.
With i-doit solutions, you benefit from
-
Structured and standardized procedures
-
Centralized documentation and verification
-
Automated process support
-
Audit and certification preparation
-
Reduction of manual effort
You can:
-
request a demo or trial version
-
book a consultation or webinar
-
introduce the software step by step - from the first status check to full compliance implementation.




