
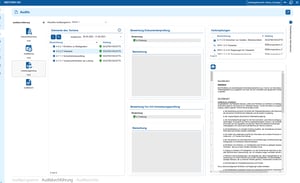
The 6 most important functions for audit management
Own audit programs can be easily compiled
The tool guides you through the audit, from document review to audit planning and implementation review
An audit report is created automatically
Derive and track tasks at the touch of a button
Quick visualization via customizable dashboards
Planning and conducting audits, from the audit to the report
How can audits be planned and carried out efficiently?
Regular internal audits are essential, but require planning, structure and follow-up. Without support, the effort involved is high and results remain difficult to compare.
i-doit offers integrated audit management: document review, audit planning and scheduling as well as implementation checks are carried out directly in the tool. Audit programs can be created individually and an audit report is always generated as a result.
Advantages:
- Audit planning, review and follow-up in one tool
- Individually configurable audit programs
- Standardized audit reports as a result
- High transparency of audit status and results

Book your personal live demo
Our i-doit team will be happy to take the time to advise you personally on your application.
Suitable add-ons
Our add-ons for modular function expansion
Create powerful automations without programming knowledge, simply start them on a schedule or manually at the touch of a button.
Automatically create documents as PDFs with daily updated data (e.g. hardware handover certificate or disaster recovery plan).
Add-on for powerful data analysis. Calculate service costs, check the data quality of the CMDB and carry out failure simulations.
Easily create forms that you can make available to users for simplified data entry. Example: Allow users to document hardware or goods themselves.
Set up an information security management system with risk analysis and management in accordance with ISO 27001.
Integrate the Checkmk2 monitoring system into i-doit. This supports comparisons between TARGET and ACTUAL from CMDB and monitoring.
Store buttons with your own triggers and start IT processes directly from i-doit - e.g. the automatic deployment of a virtual machine.
With this add-on, you can create an information security management system (ISMS) in accordance with the BSI's IT baseline protection methodology.
Related use cases
i-doit offers companies comprehensive functions and interfaces

You connect ticket systems, automation tools and monitoring systems such as Zammad or n8n directly via API.

You document workstations with devices, peripherals and responsible persons and control handovers and returns centrally.

You control audits centrally, plan audits, document results and automatically generate audit reports.

You analyze your IT infrastructure, identify documentation gaps and create location, user or cost centre-related reports and audit PDFs.

You are automatically informed about deadlines, licenses and guarantees and can keep an eye on the status and need for action.

You automatically record clients, servers, printers and peripherals and document hardware, software and QR codes centrally.

You manage users, accounts and rights centrally, document responsibilities and control access per system, including LDAP and group connections.

You document data protection incidents in compliance with the GDPR, assess risks and derive measures centrally.

You can manage documents in an audit-proof manner, version and edit them directly in the tool and use templates and import functions.

You create technical and organizational restart plans with automatic calculation of the restart times.

i-doit supports GAP analyses according to standards such as ISO 27001, ISO 9001 or NIS2, including maturity level assessment, responsibilities and document assignment.
You link tickets to affected devices, analyze causes via dependencies and monitor SLAs centrally.

You record and uniquely identify assets using QR and barcodes, create individual labels and take a mobile inventory of devices using the app and printer tool.

You document emergency concepts, system manuals, backups and disaster recovery centrally and comprehensibly.

They document maintenance and lifecycles, make changes traceable, automate processes and keep track of responsibilities and warranty periods.

You evaluate and manage suppliers centrally, document contracts and maintain contact details and replacement suppliers.

You derive measures, distribute tasks, track deadlines and receive automatic notifications by e-mail.

You integrate monitoring data directly into the IT documentation, see asset failures and link statuses to the change history.

You document active and passive network elements including cabling, port assignment, IP addresses and configurations centrally and comprehensibly.

You manage entries and exits, including device handovers, returns and referral certificates centrally.

i-doit enables protection requirement analyses with automatic inheritance into the infrastructure, risk assessment and tracking of measures.

You document and evaluate security incidents in accordance with ISO and NIS2, assign affected assets and centrally derive measures.

You record and analyze software and licenses, monitor runtimes, users and authorizations and avoid license violations and unnecessary costs.

You document locations, rooms and infrastructure, link these to contact persons and also visualize server rooms clearly.

You document and manage contracts centrally, link them to objects and responsible parties and are automatically informed about deadlines and terms.

You keep an eye on servers, VMs, dependencies and certificates centrally and automatically synchronized.




