ISMS
i-doit / Paid
Build an information security management system with risk analysis and management according to ISO 27001
-
ISO27001 Risk Management within i-doit
-
Importing and managing threats and measures from external catalogs
-
Risk evaluations directly at documented assets
-
Reporting and integration into the i-doit Add-on Documents
Support for this add-on is included in the i-doit basic support.
For installation instructions, please visit our knowledge base

IT Documentation with i-doit: the foundation for successful ISMS
Get a comprehensive overview of your (IT) infrastructure while maintaining high data quality through integrated processes.
The i-doit Add-on ISMS integrates security documentation directly into your CMDB, where it belongs. Since IT documentation is the first to know about new components and infrastructure changes, you can manage security assessments daily through risk identification and evaluation of objects (IT assets, Configuration Items) directly in i-doit.
We believe change processes are complex enough already! Avoid purchasing additional software and maintaining redundant data. The i-doit Add-on ISMS's native i-doit integration leverages existing functions like templates, bulk processing, and reporting. Users can add security information to assets without modifying the underlying data model. For final refinements to your Risk Management Process, the i-doit Add-on Documents can incorporate ISMS data into professionally formatted documents matching your corporate design.
Achieve ISO 27001 Compliance in Just Three Steps
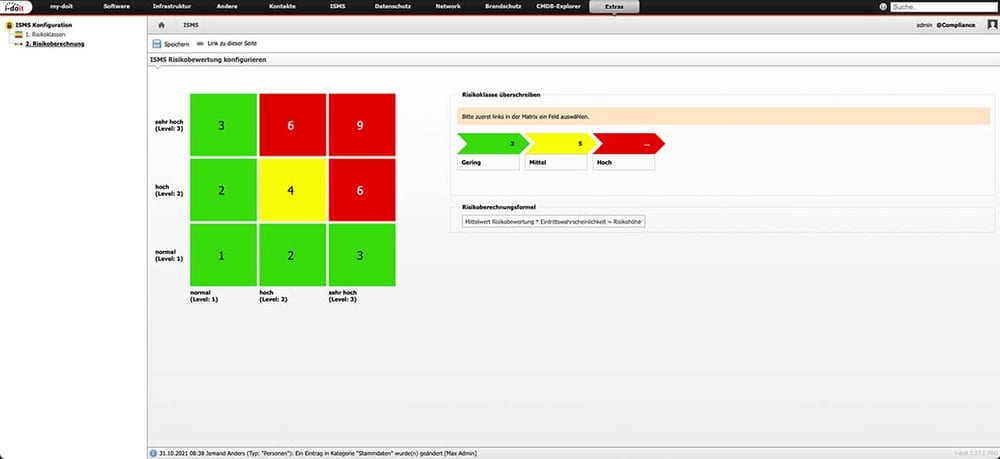
With the i-doit Add-on ISMS, you seamlessly integrate risk assessment directly into your IT asset management. Whether following ISO 27001 Annex A, the BSI IT-Grundschutz Catalog, or the IT Security Catalog of the Bundesnetzagentur, you’re covered from the start.
- Step 1: Install the i-doit Add-on ISMS and conduct risk assessments within the context of your IT assets.
- Step 2: Customize your risk management framework by adjusting predefined catalogs, defining impact scenarios, setting up mitigation measures, and assigning roles, responsibilities, and rating scales. Initial report definitions complete this phase.
- Step 3: Implement and maintain risk management to ensure ISO 27001 compliance. Analyze and evaluate assets, manage versioning, and follow the PDCA cycle (Plan, Do, Check, Act) with full documentation support from the i-doit Add-on ISMS.

Use cases
i-doit use cases for your documentation needs

You document active and passive network elements including cabling, port assignment, IP addresses and configurations centrally and comprehensibly.

You record and analyze software and licenses, monitor runtimes, users and authorizations and avoid license violations and unnecessary costs.

You analyze your IT infrastructure, identify documentation gaps and create location, user or cost centre-related reports and audit PDFs.

You document and manage contracts centrally, link them to objects and responsible parties and are automatically informed about deadlines and terms.

They document maintenance and lifecycles, make changes traceable, automate processes and keep track of responsibilities and warranty periods.

You document locations, rooms and infrastructure, link these to contact persons and also visualize server rooms clearly.
More Add-ons
Expand i-doit to include DSGVO-relevant areas. The master data remains, the extended rights system ensures security.
i-doit
Free
From the hardware handover certificate to the disaster recovery plan. Create appealing documents - also as PDF - with daily updated data from your CMDB - automatically!
i-doit
Paid
Record and control authorizations between business departments and IT. Authorizations can be linked to business applications via LDAP/LDAPs.
i-doit
Free
Build information security management systems (ISMS) according to the BSI's IT Baseline Protection methodology.
i-doit
Paid
Get your personalized quote today!
Discover how the i-doit Add-on ISMS can support and streamline your processes. Get in touch with us for more information, pricing details, or to request a quote.

Telefon: +49 (0) 211 - 699 31 0




